
One presentation outlines how the NSA performs “industrial-scale exploitation” of computer networks across the world.
Top-secret documents reveal that the National Security Agency is dramatically expanding its ability to covertly hack into computers on a mass scale by using automated systems that reduce the level of human oversight in the process.
The classified files – provided previously by NSA whistleblower Edward Snowden – contain new details about groundbreaking surveillance technology the agency has developed to infect potentially millions of computers worldwide with malware “implants.” The clandestine initiative enables the NSA to break into targeted computers and to siphon out data from foreign Internet and phone networks.
The covert infrastructure that supports the hacking efforts operates from the agency’s headquarters in Fort Meade, Maryland, and from eavesdropping bases in the United Kingdom and Japan. GCHQ, the British intelligence agency, appears to have played an integral role in helping to develop the implants tactic.
In some cases the NSA has masqueraded as a fake Facebook server, using the social media site as a launching pad to infect a target’s computer and exfiltrate files from a hard drive. In others, it has sent out spam emails laced with the malware, which can be tailored to covertly record audio from a computer’s microphone and take snapshots with its webcam. The hacking systems have also enabled the NSA to launch cyberattacks by corrupting and disrupting file downloads or denying access to websites.
The implants being deployed were once reserved for a few hundred hard-to-reach targets, whose communications could not be monitored through traditional wiretaps. But the documents analyzed by The Intercept show how the NSA has aggressively accelerated its hacking initiatives in the past decade by computerizing some processes previously handled by humans.
The automated system – codenamed TURBINE – is designed to “allow the current implant network to scale to large size (millions of implants) by creating a system that does automated control implants by groups instead of individually.”
In a top-secret presentation, dated August 2009, the NSA describes a pre-programmed part of the covert infrastructure called the “Expert System,” which is designed to operate “like the brain.” The system manages the applications and functions of the implants and “decides” what tools they need to best extract data from infected machines.
Mikko Hypponen, an expert in malware who serves as chief research officer at the Finnish security firm
F-Secure, calls the revelations “disturbing.” The NSA’s surveillance techniques, he warns, could inadvertently be undermining the security of the Internet.
“When they deploy malware on systems,” Hypponen says, “they potentially create new vulnerabilities in these systems, making them more vulnerable for attacks by third parties.”
Hypponen believes that governments could arguably justify using malware in a small number of targeted cases against adversaries. But millions of malware implants being deployed by the NSA as part of an automated process, he says, would be “out of control.”
“That would definitely not be proportionate,” Hypponen says. “It couldn’t possibly be targeted and named. It sounds like wholesale infection and wholesale surveillance.”
The NSA declined to answer questions about its deployment of implants, pointing to a new presidential policy directive announced by President Obama. “As the president made clear on 17 January,” the agency said in a statement, “signals intelligence shall be collected exclusively where there is a foreign intelligence or counterintelligence purpose to support national and departmental missions, and not for any other purposes.”
“Owning the Net”
The NSA began rapidly escalating its hacking efforts a decade ago. In 2004, according to secret
internal records, the agency was managing a small network of only 100 to 150 implants. But over the next six to eight years, as an elite unit called Tailored Access Operations (TAO) recruited new hackers and developed new malware tools, the number of implants soared to tens of thousands.
To penetrate foreign computer networks and monitor communications that it did not have access to through other means, the NSA wanted to go beyond the limits of traditional signals intelligence, or SIGINT, the agency’s term for the interception of electronic communications. Instead, it sought to broaden “active” surveillance methods – tactics designed to directly infiltrate a target’s computers or network devices.
In the documents, the agency describes such techniques as “a more aggressive approach to SIGINT” and says that the TAO unit’s mission is to “aggressively scale” these operations.
But the NSA recognized that managing a massive network of implants is too big a job for humans alone.
“One of the greatest challenges for active SIGINT/attack is scale,” explains the top-secret presentation from 2009. “Human ‘drivers’ limit ability for large-scale exploitation (humans tend to operate within their own environment, not taking into account the bigger picture).”
The agency’s solution was TURBINE. Developed as part of TAO unit, it is described in the leaked documents as an “intelligent command and control capability” that
enables “industrial-scale exploitation.”
TURBINE was designed to make deploying malware much easier for the NSA’s hackers by reducing their role in overseeing its functions. The system would “relieve the user from needing to know/care about the details,” the NSA’s Technology Directorate notes in
one secret document from 2009. “For example, a user should be able to ask for ‘all details about application X’ and not need to know how and where the application keeps files, registry entries, user application data, etc.”
In practice, this meant that TURBINE would automate crucial processes that previously had to be performed manually – including the configuration of the implants as well as surveillance collection, or “tasking,” of data from infected systems. But automating these processes was about much more than a simple technicality. The move represented a major tactical shift within the NSA that was expected to have a profound impact – allowing the agency to push forward into a new frontier of surveillance operations.
The ramifications are starkly illustrated in one undated top-secret NSA document, which describes how the agency planned for TURBINE to “increase the current capability to deploy and manage hundreds of Computer Network Exploitation (CNE) and Computer Network Attack (CNA) implants to potentially millions of implants.” (CNE mines intelligence from computers and networks; CNA seeks to disrupt, damage or destroy them.)
Eventually, the secret files indicate, the NSA’s plans for TURBINE came to fruition. The system has been operational in some capacity since at least July 2010, and its role has become increasingly central to NSA hacking operations.
Earlier reports based on the Snowden files indicate that the NSA has already deployed between 85,000 and 100,000 of its implants against computers and networks
across the world, with plans to keep on scaling up those numbers.
The intelligence community’s top-secret “Black Budget” for 2013, obtained by Snowden, lists TURBINE as part of a broader NSA surveillance initiative named “Owning the Net.”
The agency sought $67.6 million in taxpayer funding for its Owning the Net program last year. Some of the money was earmarked for TURBINE, expanding the system to encompass “a wider variety” of networks and “enabling greater automation of computer network exploitation.”
Circumventing Encryption
The NSA has a diverse arsenal of malware tools, each highly sophisticated and customizable for different purposes.
One implant, codenamed UNITEDRAKE, can be used with a variety of “plug-ins” that enable the agency to gain total control of an infected computer.
An implant plug-in named CAPTIVATEDAUDIENCE, for example, is used to take over a targeted computer’s microphone and record conversations taking place near the device. Another, GUMFISH, can covertly take over a computer’s webcam and snap photographs. FOGGYBOTTOM records logs of Internet browsing histories and collects login details and passwords used to access websites and email accounts. GROK is used to log keystrokes. And SALVAGERABBIT exfiltrates data from removable flash drives that connect to an infected computer.
The implants can enable the NSA to circumvent privacy-enhancing encryption tools that are used to browse the Internet anonymously or scramble the contents of emails as they are being sent across networks. That’s because the NSA’s malware gives the agency unfettered access to a target’s computer before the user protects their communications with encryption.
It is unclear how many of the implants are being deployed on an annual basis or which variants of them are currently active in computer systems across the world.
Previous reports
have alleged that the NSA worked with Israel to develop the Stuxnet malware, which was used to sabotage Iranian nuclear facilities. The agency also
reportedly worked with Israel to deploy malware called Flame to infiltrate computers and spy on communications in countries across the Middle East.
According to the Snowden files, the technology has been used to seek out terror suspects as well as individuals regarded by the NSA as “extremist.” But the mandate of the NSA’s hackers is not limited to invading the systems of those who pose a threat to national security.
In one secret post on an internal message board, an operative from the NSA’s Signals Intelligence Directorate describes using malware attacks against systems administrators who work at foreign phone and Internet service providers. By hacking an administrator’s computer, the agency can gain covert access to communications that are processed by his company. “Sys admins are a means to an end,” the NSA operative writes.
The internal post – titled “I hunt sys admins” – makes clear that terrorists aren’t the only targets of such NSA attacks. Compromising a systems administrator, the operative notes, makes it easier to get to other targets of interest, including any “government official that happens to be using the network some admin takes care of.”
Similar tactics have been adopted by Government Communications Headquarters, the NSA’s British counterpart. As the German newspaper
Der Spiegel reported in September, GCHQ hacked computers belonging to network engineers at Belgacom, the Belgian telecommunications provider.
The mission, codenamed “Operation Socialist,” was designed to enable GCHQ to monitor mobile phones connected to Belgacom’s network. The secret files deem the mission a “success,” and indicate that the agency had the ability to covertly access Belgacom’s systems since at least 2010.
Infiltrating cellphone networks, however, is not all that the malware can be used to accomplish. The NSA has specifically tailored some of its implants to infect large-scale network routers used by Internet service providers in foreign countries. By compromising routers – the devices that connect computer networks and transport data packets across the Internet – the agency can gain covert access to monitor Internet traffic, record the browsing sessions of users, and intercept communications.
Two implants the NSA injects into network routers, HAMMERCHANT and HAMMERSTEIN, help the agency to intercept and perform “exploitation attacks” against data that is sent through a
Virtual Private Network, a tool that uses encrypted “tunnels” to enhance the security and privacy of an Internet session.
The implants also track phone calls sent across the network via Skype and other Voice Over IP software, revealing the username of the person making the call. If the audio of the VOIP conversation is sent over the Internet using unencrypted “Real-time Transport Protocol” packets, the implants can covertly record the audio data and then return it to the NSA for analysis.
But not all of the NSA’s implants are used to gather intelligence, the secret files show. Sometimes, the agency’s aim is disruption rather than surveillance. QUANTUMSKY, a piece of NSA malware developed in 2004, is used to block targets from accessing certain websites. QUANTUMCOPPER, first tested in 2008, corrupts a target’s file downloads. These two “attack” techniques are revealed on
a classified list that features nine NSA hacking tools, six of which are used for intelligence gathering. Just one is used for “defensive” purposes – to protect U.S. government networks against intrusions.
“Mass exploitation potential”
Before it can extract data from an implant or use it to attack a system, the NSA must first install the malware on a targeted computer or network.
According to
one top-secret document from 2012, the agency can deploy malware by sending out spam emails that trick targets into clicking a malicious link. Once activated, a “back-door implant” infects their computers within eight seconds.
There’s only one problem with this tactic, codenamed WILLOWVIXEN: According to the documents, the spam method has become less successful in recent years, as Internet users have become wary of unsolicited emails and less likely to click on anything that looks suspicious.
Consequently, the NSA has turned to new and more advanced hacking techniques. These include performing so-called “man-in-the-middle” and “man-on-the-side” attacks, which covertly force a user’s internet browser to route to NSA computer servers that try to infect them with an implant.
To perform a man-on-the-side attack, the NSA observes a target’s Internet traffic using its global network of covert “accesses” to data as it flows over fiber optic cables or satellites. When the target visits a website that the NSA is able to exploit, the agency’s surveillance sensors
alert the TURBINE system, which then “shoots” data packets at the targeted computer’s IP address within a fraction of a second.
In one man-on-the-side technique, codenamed QUANTUMHAND, the agency disguises itself as a fake Facebook server. When a target attempts to log in to the social media site, the NSA transmits malicious data packets that trick the target’s computer into thinking they are being sent from the real Facebook. By concealing its malware within what looks like an ordinary Facebook page, the NSA is able to hack into the targeted computer and covertly siphon out data from its hard drive. A top-secret animation demonstrates the tactic in action.
The documents show that QUANTUMHAND became operational in October 2010, after being successfully tested by the NSA against about a dozen targets.
According to Matt Blaze, a surveillance and cryptography expert at the University of Pennsylvania, it appears that the QUANTUMHAND technique is aimed at targeting specific individuals. But he expresses concerns about how it has been covertly integrated within Internet networks as part of the NSA’s automated TURBINE system.
“As soon as you put this capability in the backbone infrastructure, the software and security engineer in me says that’s terrifying,” Blaze says.
“Forget about how the NSA is intending to use it. How do we know it is working correctly and only targeting who the NSA wants? And even if it does work correctly, which is itself a really dubious assumption, how is it controlled?”
In an email statement to The Intercept, Facebook spokesman Jay Nancarrow said the company had “no evidence of this alleged activity.” He added that Facebook implemented HTTPS encryption for users last year, making browsing sessions less vulnerable to malware attacks.
Nancarrow also pointed out that other services besides Facebook could have been compromised by the NSA. “If government agencies indeed have privileged access to network service providers,” he said, “any site running only [unencrypted] HTTP could conceivably have its traffic misdirected.”
A man-in-the-middle attack is a similar but slightly more aggressive method that can be used by the NSA to deploy its malware. It refers to a hacking technique in which the agency covertly places itself between computers as they are communicating with each other.
This allows the NSA not only to observe and redirect browsing sessions, but to modify the content of data packets that are passing between computers.
The man-in-the-middle tactic can be used, for instance, to covertly change the content of a message as it is being sent between two people, without either knowing that any change has been made by a third party. The same technique is
sometimes used by criminal hackers to defraud people.
A top-secret NSA presentation from 2012 reveals that the agency developed a man-in-the-middle capability called SECONDDATE to “influence real-time communications between client and server” and to “quietly redirect web-browsers” to NSA malware servers called FOXACID. In October, details about the FOXACID system were
reported by the Guardian, which revealed its links to attacks against users of the Internet anonymity service Tor.
But SECONDDATE is tailored not only for “surgical” surveillance attacks on individual suspects. It can also be used to launch bulk malware attacks against computers.
According to the 2012 presentation, the tactic has “mass exploitation potential for clients passing through network choke points.”
Blaze, the University of Pennsylvania surveillance expert, says the potential use of man-in-the-middle attacks on such a scale “seems very disturbing.” Such an approach would involve indiscriminately monitoring entire networks as opposed to targeting individual suspects.
“The thing that raises a red flag for me is the reference to ‘network choke points,’” he says. “That’s the last place that we should be allowing intelligence agencies to compromise the infrastructure – because that is by definition a mass surveillance technique.”
To deploy some of its malware implants, the NSA exploits security vulnerabilities in commonly used Internet browsers such as Mozilla Firefox and Internet Explorer.
The agency’s hackers also exploit security weaknesses in network routers and in popular software plugins such as Flash and Java to deliver malicious code onto targeted machines.
The implants can circumvent anti-virus programs, and the NSA has gone to extreme lengths to ensure that its clandestine technology is extremely difficult to detect. An implant named VALIDATOR, used by the NSA to upload and download data to and from an infected machine, can be set to self-destruct – deleting itself from an infected computer after a set time expires.
In many cases, firewalls and other security measures do not appear to pose much of an obstacle to the NSA. Indeed, the agency’s hackers appear confident in their ability to circumvent any security mechanism that stands between them and compromising a computer or network. “If we can get the target to visit us in some sort of web browser, we can probably own them,” an agency hacker boasts in one secret document. “The only limitation is the ‘how.’”
Covert Infrastructure
The TURBINE implants system does not operate in isolation.
The NSA’s headquarters in Maryland are part of this network, as are eavesdropping bases used by the agency in Misawa, Japan and Menwith Hill, England.
The sensors, codenamed TURMOIL, operate as a sort of high-tech surveillance dragnet, monitoring packets of data as they are sent across the Internet.
When TURBINE implants exfiltrate data from infected computer systems, the TURMOIL sensors automatically identify the data and return it to the NSA for analysis. And when targets are communicating, the TURMOIL system can be used to send alerts or “tips” to TURBINE, enabling the initiation of a malware attack.
The NSA identifies surveillance targets based on a series of data “selectors” as they flow across Internet cables. These selectors, according to internal documents, can include email addresses, IP addresses, or the unique “cookies” containing a username or other identifying information that are sent to a user’s computer by websites such as Google, Facebook, Hotmail, Yahoo, and Twitter.
Other selectors the NSA uses can be gleaned from unique Google advertising cookies that track browsing habits, unique encryption key fingerprints that can be traced to a specific user, and computer IDs that are sent across the Internet when a Windows computer crashes or updates.
What’s more, the TURBINE system operates with the knowledge and support of other governments, some of which have participated in the malware attacks.
Classification markings on the Snowden documents indicate that NSA has shared many of its files on the use of implants with its counterparts in the so-called Five Eyes surveillance alliance – the United Kingdom, Canada, New Zealand, and Australia.
GCHQ, the British agency, has taken on a particularly important role in helping to develop the malware tactics. The Menwith Hill satellite eavesdropping base that is part of the TURMOIL network, located in a rural part of Northern England, is operated by the NSA in close cooperation with GCHQ.
Top-secret documents show that the British base – referred to by the NSA as “MHS” for Menwith Hill Station – is an integral component of the TURBINE malware infrastructure and has been used to
experiment with implant “exploitation” attacks against users of Yahoo and Hotmail.
In
one document dated 2010, at least five variants of the QUANTUM hacking method were listed as being “operational” at Menwith Hill. The same document also reveals that GCHQ helped integrate three of the QUANTUM malware capabilities – and test two others – as part of a surveillance system it operates codenamed INSENSER.
GCHQ cooperated with the hacking attacks despite having reservations about their legality. One of the Snowden files,
previously disclosed by Swedish broadcaster SVT, revealed that as recently as April 2013, GCHQ was apparently reluctant to get involved in deploying the QUANTUM malware due to “legal/policy restrictions.” A representative from a unit of the British surveillance agency, meeting with an obscure telecommunications standards committee in 2010, separately
voiced concerns that performing “active” hacking attacks for surveillance “may be illegal” under British law.
In response to questions from The Intercept, GCHQ refused to comment on its involvement in the covert hacking operations. Citing its boilerplate response to inquiries, the agency said in a statement that “all of GCHQ’s work is carried out in accordance with a strict legal and policy framework which ensures that our activities are authorized, necessary and proportionate, and that there is rigorous oversight.”
Whatever the legalities of the United Kingdom and United States infiltrating computer networks, the Snowden files bring into sharp focus the broader implications. Under cover of secrecy and without public debate, there has been an unprecedented proliferation of aggressive surveillance techniques. One of the NSA’s primary concerns, in fact, appears to be that its clandestine tactics are now being adopted by foreign rivals, too.
“Hacking routers has been good business for us and our 5-eyes partners for some time,” notes one NSA analyst in
a top-secret document dated December 2012. “But it is becoming more apparent that other nation states are honing their skillz [sic] and joining the scene.”

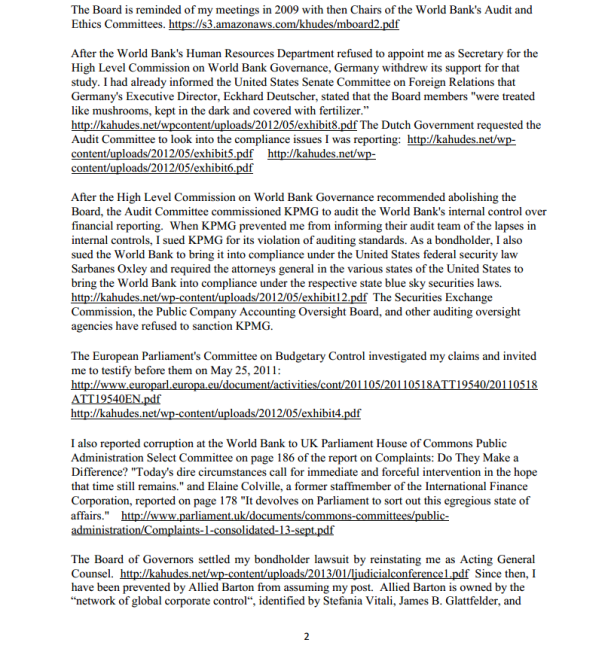













 One presentation outlines how the NSA performs “industrial-scale exploitation” of computer networks across the world.
One presentation outlines how the NSA performs “industrial-scale exploitation” of computer networks across the world.





